DevOps is critical to an organization’s cybersecurity fabric, with those with strong DevOps deployments discovering bugs 11 times faster than those without, according to research.
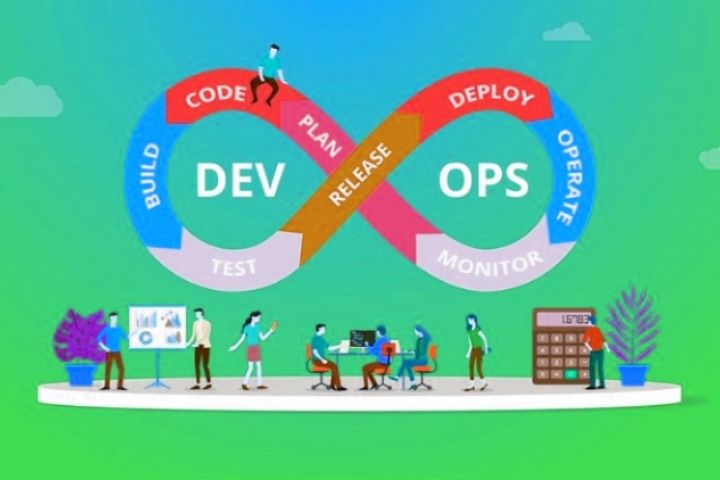
The report outlined the following five components required for a successful DevOps implementation within an organization, protecting the organization’s infrastructure and lengthening its software lifecycle.
- Collective responsibility – Everyone has their own security responsibility and should be aware of their own contribution to the organization’s security posture. Edge users and developers are not only “security conscious” but they are the first line of defense.
- Collaboration and integration: A culture of safety and collaboration is necessary for members of all functional teams to report potential anomalies.
- Pragmatic Implementation: Adopting a framework-independent digital privacy and security model that focuses on application development will allow organizations to approach DevOps security in a pragmatic way.
- Automation – Software quality can be improved by improving the thoroughness, timeliness and frequency of testing / feedback. Processes that can be automated should be, and those that cannot be considered should be eliminated.
- Measure, Monitor, Report, and Act: For DevOps to be successful, software development and post-delivery results must be continuously measured, monitored, reported, and applied by the right people at the right time.
DevOps: The Future of DevOps Security
One way DevOps improves developer productivity is by allowing developers to recycle code from previous projects or open source repositories like GitHub. However, without proper analysis and disinfection, these codes can pose a threat to an application.
When you deploy your code in the cloud, you cannot use traditional security services. You need to rethink your security strategy. DevOps teams leverage multiple platforms, from server less computing to microservices and multi-cloud in their applications. There is no one-size-fits-all solution for protecting cloud-native applications. These applications are highly distributed and multi-component, so organizations need a multifaceted approach to better protect these applications.
Cloud-native applications are continually integrated and deployed, making it difficult for security teams to identify and mitigate risks. Traditional security tools cannot match the speed, scale, and dynamics of cloud-native applications, rendering them useless.
By following the DevOps approach, security professionals need to create privileged accounts and login details and share them on corporate networks automatically. With server less applications and the cloud, security teams do not have a traditional location like the operating system to enforce security policies. A large amount of useful data, such as keys, storage account credentials, secrets, database passwords, and built-in passwords, are stored in the repositories. It is crucial that this information is kept extremely secure, as attackers can use this information to cause serious harm.
Using containerized open source software can lead to increased vulnerabilities. DevOps teams must ensure that rogue containers are not used in production. Attackers can use these containers to launch an application-wide attack.
In traditional applications, security has a lower priority and security policies are always used after development is complete. But with DevOps, security can’t be an afterthought. Businesses that rely on a DevOps approach must make security their top priority. One of the ways to ensure that security is at the core of a DevOps implementation is a DevOps security stack. To employ the DevOps security stack, IT teams should no longer be excluded from the team.
Involving security experts can help them understand what the application is and how it should work so that they can identify risks and take steps to mitigate them. This approach has become popular. DevOps is a collaboration between development, security, and operations teams working together to ensure that security is at the root of an application, not just on the surface.